Homakov: Story of a White Hat
In early March 2012, a Russian programmer one month shy of his 19th birthday emerged on the radar of the software world via one “simple” commit that startled both the Rails and GitHub communities.

The exploited vulnerability was known to many in the community, so discussion about the controversy gravitated towards GitHub’s failure to properly protect repos and the potentially insecure default settings of Rails. The attention drawn to mass assignment served as a beneficial public service announcement to other Rails users, although the delivery method put off many developers as well as GitHub admins who quickly suspended (and just as quickly reinstated) the account. It was all over within a few hours, but Homakov had “arrived”.
Who is this guy?
Egor Homakov grew up in Saransk, a small city of 300,000 residents that sits 400 miles east of Moscow and somewhere deep within Ukraine on a Risk board. He dabbled with Delphi as a teenager to learn how programs worked, and later Pascal. His GitHub dates to 2009, oddly enough on New Year’s Eve. After initially struggling to understand programming concepts, his self-study turned a corner when he transitioned to web apps. Homakov dropped out of university before completing a year, which he admits was a risky move for someone in Saransk, but he found the program far too boring to continue.
Homakov initially focused his career on SEO, but when clients were hard to come by he began advertising PHP programming services on SEO forums. When negotiating a proposal to build a simple news management system for an early prospective client, Homakov requested a rate around $10 per hour. The prospect countered with an offer of $30 if the job was done well. This was a significant wage in Saransk, and Homakov distinctly remembers his mother’s pride.
Over the next few years Homakov bounced between employers, with freelancing gigs followed by short stints at European startups in the online payments and travel spaces. Eventually he decided consulting was his best option, and he is now part of the security firm Sakurity which provides penetration testing and code audit services to clients worldwide. The lion’s share of Homakov’s income comes from consulting, with some additional income via bug bounties (including a $4,000 payout from GitHub earlier this year).
Fame or infamy
Although he admits that he knew little about security before the 2012 GitHub hack, Homakov instantly became a polarizing figure. His action was lauded by some who believed the high profile exposure of the vulnerability would benefit the community by raising awareness for other Rails users. Others felt a more private notification would have been more appropriate, not to mention GitHub’s clear responsible disclosure policy in the terms of service. Supporters saw him as some populist hero sparring the Rails elite, while detractors resorted to mocking his broken English and even criticizing his profile photos. Those on both sides surely realized that he could have chosen the black hat route and done something much more malicious with the Rails repo and any others, and could have done so anonymously.
Some soon discovered that Homakov had indeed opened an issue about the mass assignment vulnerability, and only went public when he felt his warning had fallen on deaf ears. Homakov later regretted much of his behavior, and eventually provided a brief public apology to both GitHub and the Rails team. It’s not much of a stretch to imagine that GitHub’s bug bounty program launched earlier this year was at least partially influenced by their highly public experience with Homakov.
The most interesting man in tech?
Since leaving Russia, Homakov has become a world traveler. His Tumblr feed reads like a poorly edited and NSFW Frommer’s guide, chock full of selfies and commentary on the livability and food/drink from locations throughout Europe, the United States, and southeast Asia. Sofia, St. Petersburg, Barcelona, Istanbul, New York, Shanghai, and Seoul – all while earning a living and developing a reputation in the security space.
From his writing it is clear that he has an affinity for Asian culture, bright city lights, and beer (not necessarily in that order), while showing no affection for his country of birth. After about a year on the road, Homakov finally settled in Thailand, where he intends on living for a year before picking up for more travel on the spots he has missed on his first world tour. India, Africa, and South America are on the agenda.
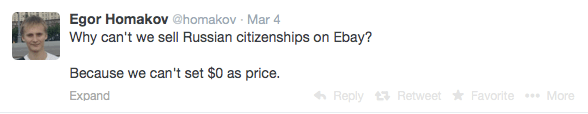
He seems pretty funny too. His Twitter feed is peppered with various self-deprecating third person references as well as little gems like this…
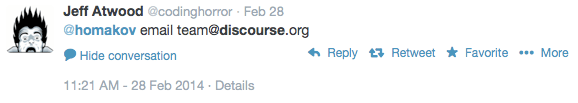
And now that he’s showing maturity…
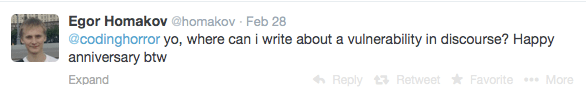 … he seems to have the ear of at least some in the industry.
… he seems to have the ear of at least some in the industry.
Although much of his security research is unpaid and he is far from wealthy, it’s been quite a trip so far. From $30 to $300 an hour, and from Russia to Bangkok with plenty of stops in between – all in two years. He admits he acted irresponsibly, but now calls himself white hat and takes responsible disclosure seriously. As someone who first arrived to the security field conspicuously, Homakov continues to strive for increased credibility and legitimacy from peers in the industry. For many, his work will speak for itself. As he now approaches his 21st birthday, one has to wonder what his future hold.
Author’s Note: This article is a departure from Job Tips For Geeks normal content, but I see value in profiling technologists who have unique careers. I hope to profile others with non-traditional backgrounds and career paths. Feel free to contact me if you feel you fit into this category.
Thanks, great story. Of course, it makes me feel like a moron because I couldn’t have so much as pulled off an SQL Injection attack at age 21, and that was a long time ago. Good for him for learning quickly.
Thanks for reading. I think there are some lessons to be learned from his story.